Forums
-
English Forum
-
Products for Home
- Kaspersky: Basic, Standard, Plus, Premium
- Kaspersky Internet Security
- Kaspersky Total Security
- Kaspersky Security Cloud
- Kaspersky Safe Kids
- Kaspersky Anti-Virus
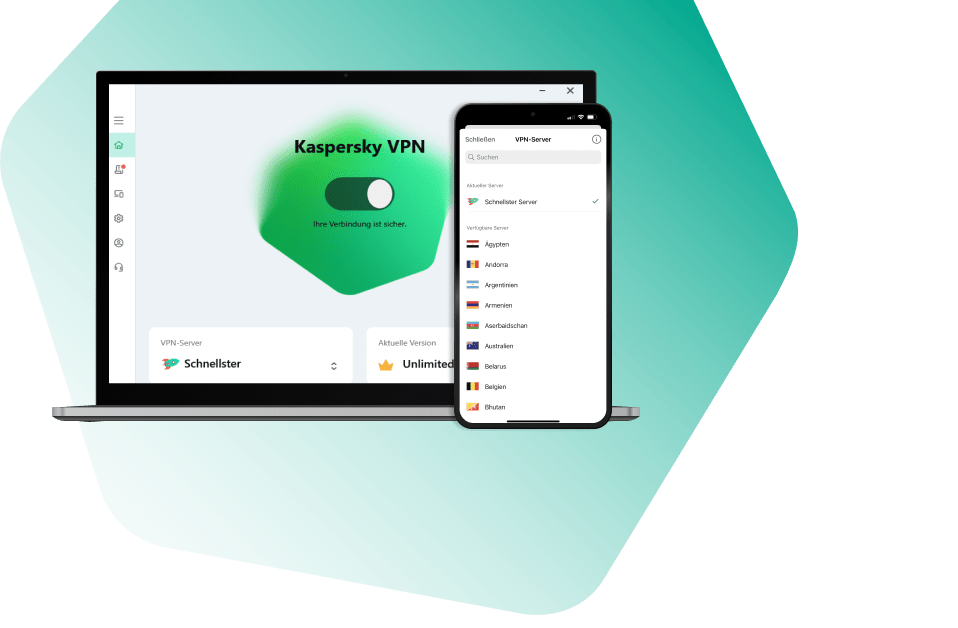
- Kaspersky VPN Secure Connection
- Kaspersky Password Manager
- Kaspersky Free
- Kaspersky Rescue Disk
- Kaspersky Virus Removal Tool
- My Kaspersky
- Virus and Ransomware related questions
- 50.8k
- posts
-
Products for Business
- Kaspersky Endpoint Security for Business
- Kaspersky Hybrid Cloud Security
- Kaspersky Security Center
- Kaspersky EDR Optimum
- Kaspersky Anti Targeted Attack & EDR Expert
- Kaspersky Endpoint Security Cloud
- Kaspersky Small Office Security & Management Console
- Kaspersky Security for Mail Server
- Kaspersky Security for Internet Gateway
- Kaspersky Security for Microsoft 365
- Kaspersky Embedded Systems Security
- Kaspersky Services
- Kaspersky Industrial Cybersecurity
- Kaspersky Scan Engine
- Kaspersky Security Awareness
- Kaspersky Unified Monitoring and Automation
- Kaspersky SD-WAN
- Kaspersky SDKs
- 9.1k
- posts
-
- 479
- posts
-
- 83
- posts
-
-
Русскоязычный форум
-
Продукты для дома
- Kaspersky: Basic, Standard, Plus, Premium
- Kaspersky Internet Security
- Kaspersky Free
- Kaspersky Total Security
- Kaspersky Secure Connection
- Kaspersky Password Manager
- Kaspersky Security Cloud
- Kaspersky Anti-Virus
- Kaspersky Safe Kids
- Kaspersky Rescue Disk
- Kaspersky Virus Removal Tool
- My Kaspersky
- Вопросы, связанные с вирусами и шифровальщиками
- 20.1k
- posts
-
Продукты для бизнеса
- Kaspersky Endpoint Security для бизнеса
- Kaspersky Hybrid Cloud Security
- Kaspersky Security Center
- Kaspersky EDR Optimum
- Kaspersky Anti Targeted Attack & EDR Expert
- Kaspersky Endpoint Security Cloud
- Kaspersky Small Office Security и Центр управления
- Kaspersky Security for Mail Server
- Kaspersky Security for Internet Gateway
- Kaspersky Security for Microsoft 365
- Kaspersky Embedded Systems Security
- Сервисы Kaspersky
- Kaspersky Industrial Cybersecurity
- Kaspersky Scan Engine
- Kaspersky Security Awareness
- Kaspersky Unified Monitoring and Automation
- Kaspersky SD-WAN
- Kaspersky SDKs
- 14k
- posts
-
- 264
- posts
-
- 49
- posts
-
- 145
- posts
-
-
Deutschsprachiges Benutzer-Forum
-
Forum para usuarios hispanohablantes
-
- 6.3k
- posts
-
- Devolución
- By harlan4096,
-
- 1.4k
- posts
-
-
Forum des Utilisateurs Français
-
- 3.7k
- posts
-

- Arnaque nexway
- By Berny,
-
- 819
- posts
-
-
Forum in Italiano
-
- 2.1k
- posts
-
- 250
- posts
-
-
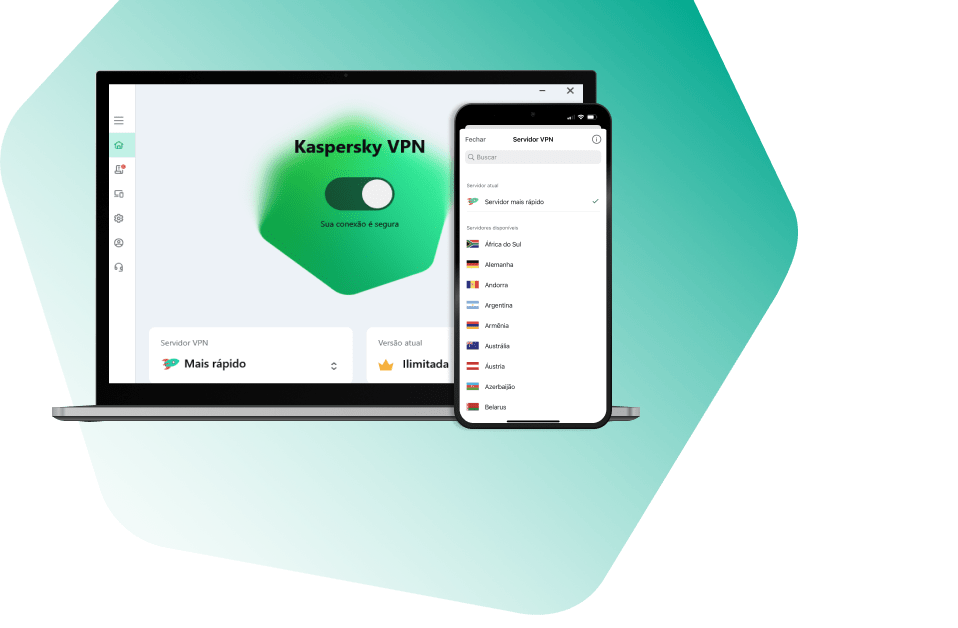
Fórum Brasileiro
-
- 2.6k
- posts
-
- 592
- posts
-
-
中文论坛
-
Nederlands Gebruikersforum
-
- 484
- posts
-
- 3
- posts
-
-
Türkçe Forum
-
- 1.4k
- posts
-
- 49
- posts
-
-
Forum Knowledgebase
-
- 2
- posts
-
- 18
- posts
-
-
Who's Online 7 Members, 0 Anonymous, 233 Guests (See full list)
-
Forum Statistics
27.2k
Total Topics151.5k
Total Posts -
Member Statistics