All Activity
- Past hour
-

Не открываются некоторые сайты после принятия нового пользовательского соглашения KSeC (10-17.03.2026)
kmscom replied to Embler's topic in Kaspersky Secure Connection
Они не всевидящие и не телепаты. Учитесь точно и твердо излагать вопрос )))). Это в жизни всегда полезно. А типа вы сами знаете куда вам идти, сами знаете что мне принести - это не прокатит. ))) -

Проблема загрузки в ChatGPT файлов и доступ к Gemini
kmscom replied to SRR's topic in Kaspersky Secure Connection
Создайте запрос в техподдержку -
A.S.R. started following Проблема загрузки в ChatGPT файлов и доступ к Gemini
-
Проблема загрузки в ChatGPT файлов и доступ к Gemini
A.S.R. replied to SRR's topic in Kaspersky Secure Connection
Ребята, Gemini теперь все? Нам из РФ туда не пробиться? Никто не нашел решение? Раньше сидела с SC. Потом он накрылся, перешла на альтернативное решение, но альтернативному 2 дня назад пришел каюк. Для работы нужен позарез. С нашими недо-альтернативами в графике трачу время раз в 10 больше, а иногда вообще хоть упор художнику заказ делать. -
KESL 12.4 под управлением KSC (linux) 15.1
Андрей Викторович replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
офигенно! "Можем а зачем" Сразу бы сказали на форуме специалисты могут решить свои проблемы сами собой.. А то такая предыстория... Так и напишите, что это форум взаимопомощи -

KESL 12.4 под управлением KSC (linux) 15.1
andrew75 replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
я не работаю с корпоративными продуктами, поэтому ничем вам не помогу в данном случае. на форуме могут помочь другие пользователи. Если они сталкивались с подобными проблемами и знают как их решить. Вам могут ответить и сотрудники компании или техподдержки. Но в случае с корпоративными продуктами это бывает редко. https://forum.kaspersky.com/guidelines/ -
cahitu48 joined the community
-
KESL 12.4 под управлением KSC (linux) 15.1
Андрей Викторович replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
Да я знаю ... Мы уже общаемся ... Можете ссылку скинуть как перенести параметры политик... ? Я не хочу в очередной раз смотря на одну консоль переносить значения в другую, тем паче я увидел, что настройки политик существенно изменились. А зачем форум? Почему под Windows 12.12 нормально пролонгировались политики с 12.X ? А для чего существует данный форум? *****@*****.tld -
Не открываются некоторые сайты после принятия нового пользовательского соглашения KSeC (10-17.03.2026)
10032026P replied to Embler's topic in Kaspersky Secure Connection
Спустя 8 дней после обращения по вопросу возврата денежных средств лаборатория Касперского продолжает ломать комедию. Ничего лучше не придумали, как включить дурака, якобы не видят номер заказа и данные о покупателе, а из текста обращения не удалось установить о каком продукте идёт речь. -

KESL 12.4 под управлением KSC (linux) 15.1
andrew75 replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
служба поддержки существует для того, чтобы решать проблемы пользователей при использовании продуктов. Поэтому это странная позиция. -

Renovacion suscripcion
harlan4096 replied to expertstravelservices's topic in Para usuarios particulares
¿Por favor indica dónde estás residiendo actualmente? Pagos en Venezuela deberían ser admitidos. -
KESL 12.4 под управлением KSC (linux) 15.1
Андрей Викторович replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
Я это понимаю, но ответственные сотрудники Россети-Сибирь ответили мне, что это не является проблемой, чтобы напрягать службу поддержки. Я вот прочитав все решения по установке и развертыванию KESL считаю скриптовый механизм развертыания неправильный. Если мы пользуемся групповыми политиками. Я ими пользуюсь для первоначальной установки агента. Я создал свой rpm пакет для первоначальной установки агента. postinstall передаются параметры.. Но вопрос то был не в Этом. Да я потом задачами KSC обновляю первоначальный агент. - Today
-
dantey1993 joined the community
-

KESL 12.4 под управлением KSC (linux) 15.1
andrew75 replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
Это первое что надо было сделать. На форуме отвечают такие же пользователи как и вы. Не факт что кто-то сталкивался с такой же проблемой. -
KESL 12.4 под управлением KSC (linux) 15.1
Андрей Викторович replied to Андрей Викторович's topic in Kaspersky Endpoint Security для бизнеса
Если необходимо по данному обращению написать обращение в support. Напишете -
Андрей Викторович started following Kaspersky Endpoint Security для бизнеса
-
Андрей Викторович started following KESL 12.4 под управлением KSC (linux) 15.1
-
KESL 12.4 под управлением KSC (linux) 15.1
Андрей Викторович posted a topic in Kaspersky Endpoint Security для бизнеса
Добрый день. В нашем предприятии установлен KSC Linux 15.1 Я решил на рабочих станциях под управлением linux обновить агента администрирования до версии 16.1 и KESL до версии 12.4. Обновление прошло успешно, но я столкнулся с тем, что KESL 12.4 не понимает политики для версии 12.1. Как правильно перенести правила политики 12.1 в политики для 12.4 ? Очень уж много наработок сделано. Есть ли каки-то рекомендации? Заранее признателен. -
bulichvs started following Добавить файл в исключения
-
Добрый день! Помогите разобраться, как добавить файл в исключения через консоль Kaspersky security center 15.1.0.20748. На одном из компьютеров, на котором установлен Kaspersky endpoint security 12.8.0.505, один файл обозначен, как вредоносный. Также об этом появилось сообщение на консоли KSC в разделе Активные угрозы. Если я заведомо знаю, что этот файл не опасный, как я могу его добавить в исключения через консоль KSC? Сейчас в политике в разделе Общие настройки - Исключения и типы объектов в обоих меню Исключения из проверки и Доверенные приложения добавлены пути к конкретно этому файлу, на который ругается Kaspersky endpoint security (скриншоты). Как я понимаю, создание правила исключения в этих меню влияет только на последующие проверки на вирусы. Но не понятно одно, как теперь из меню Активные угрозы в консоли KSC убрать сообщение о найденном вредоносном файле. В консоли я могу только лечить или удалить файл, но в этом случае файл пропадет на клиентском компьютере, а это плохо. И выходит, что файл все еще ждёт каких-либо действий, но все что можно сделать это удалить его, а удалять не нужно. Как быть в этой ситуации?
-
Прямая ссылка на krd.iso образ для скачавания через wget
dom7801 replied to dom7801's topic in Kaspersky Rescue Disk
Я не знал про эту ссылку. Спасибо большое! -

Прямая ссылка на krd.iso образ для скачавания через wget
kmscom replied to dom7801's topic in Kaspersky Rescue Disk
а чем вас не устраивает ссылка на странице https://support.kaspersky.ru/utility ? -
qiu joined the community
-
 Fernando Moreira changed their profile photo
Fernando Moreira changed their profile photo -
dom7801 started following Прямая ссылка на krd.iso образ для скачавания через wget
-
Прямая ссылка на krd.iso образ для скачавания через wget
dom7801 posted a topic in Kaspersky Rescue Disk
Здравствуйте. Подскажите, пжт, прямую ссылку для скачивания через wget. Хотелось бы, чтобы скрипт выкачивал самостоятельно krd.iso -
dom7801 joined the community
-
GennadyS joined the community
-
Fernando Moreira started following open vpn
-
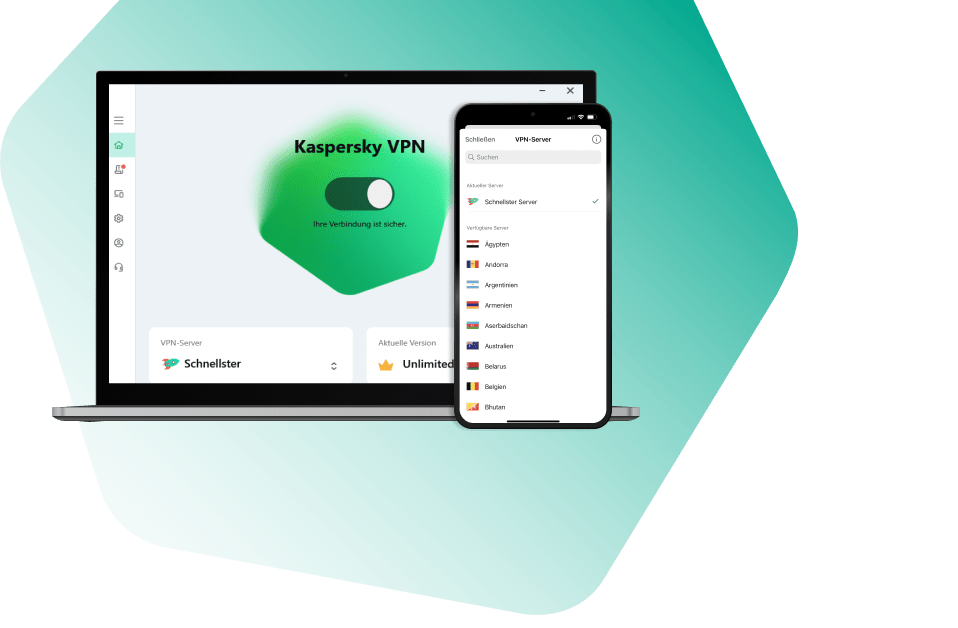
Não bati mais cabeça... Pra solução rápida instalei o Kaspersky VPN Secure Connection em uma VM Android e com o app Every Proxy roteio a VPN para os navegadores via Proxy Socks e HTTP na mesma subrede.
-
Marcelo Pacheco joined the community
-
Unable to launch steam or epic games or valorant while the app is active
Friend replied to wildilyuz's topic in Ev için
Maybe someone will be interested: https://eap.kaspersky.com/topic/6789/ -
Не отправляется запрос на е-мейл службы поддержки.
Aleksandrter replied to Aleksandrter's topic in Kaspersky: Basic, Standard, Plus, Premium
Благодарю! Капча появилась. -
Apokatapsis joined the community
-
Berny started following Subscription Expired
-
Алекс_11 joined the community
-
Hello @MightierPen, Thank you for posting back! (ioo) it's still worth contacting Kaspersky Customer Service - Kaspersky Safe Kids offers a free 7-day Trial version, *maybe* they will agree to offer that - it's worth a shot - you have nothing to loose by asking. Thank you🙏 Flood🐳+🐋
-
MightierPen started following Subscription Expired
-
I see on the Premium pricing page at the bottom it says Safe Kids one year free. That explains it because I got the premium more than a year ago. Guess I won't be getting the trial then.
-
Berny started following Warning from strange email
-
zubzero1997 joined the community
-

Подмена сертификатов FTPS TLS v1.3
andrew75 replied to Danila_iva's topic in Kaspersky: Basic, Standard, Plus, Premium
Таким образом работает проверка защищенных соединений. Антивирус расшифровывает трафик, проверяет его, затем шифрует своим сертификатом и отдает соответствующему приложению. Поэтому это приложение видит сертификат Касперского. -
NicoMOR joined the community
-
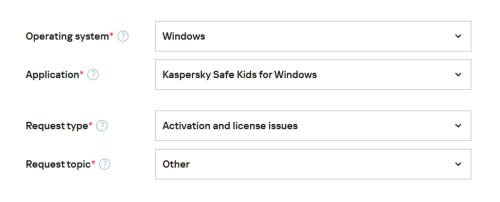
Hello @Mightier Pen, Welcome! Kaspersky *Premium* includes Kaspersky Safe Kids *Premium*. Because the image has blocked out information & an inactive subscription it's impossible to see clearly what's going on, please contact Kaspersky Customer Service https://support.kaspersky.com/b2c#contacts, on the support page select Email, fill in the template as shown, please provide a *detailed-history* & do not select the AI-Bot to submit the request: Thank you🙏 Flood🐳+🐋
-
Андрей Викторович started following Релиз Kaspersky Endpoint Security для Linux 12.4
-
Релиз Kaspersky Endpoint Security для Linux 12.4
Андрей Викторович replied to Demiad's topic in Kaspersky Endpoint Security для бизнеса
Добрый день. В нашем предприятии установлен KSC Linux 15.1 Я решил на рабочих станциях под управлением linux обновить агента администрирования до версии 16.1 и KESL до версии 12.4. Обновление прошло успешно, но я столкнулся с тем, что KESL 12.4 не понимает политики для версии 12.1. Как правильно перенести правила политики 12.1 в политики для 12.4 ? Очень уж много наработок сделано. Есть ли каке рекомендации? Заранее признателен.