
Kaspersky Plus
Güvenlik. Performans. Gizlilik. Hepsi kullanımı kolay tek bir uygulamada.

Kaspersky Small Office Security
Küçük ölçekli işletmenizi kolayca koruyun

Kaspersky Password Manager
Parolalarınız ve belgeleriniz her zaman elinizin altında

Kaspersky Small Office Security
Unkomplizierter Schutz für kleine Unternehmen

Premiumversion
Kaspersky Safe Kids
Behalten Sie Ihre Kinder im Auge, auch wenn Sie nicht in der Nähe sind
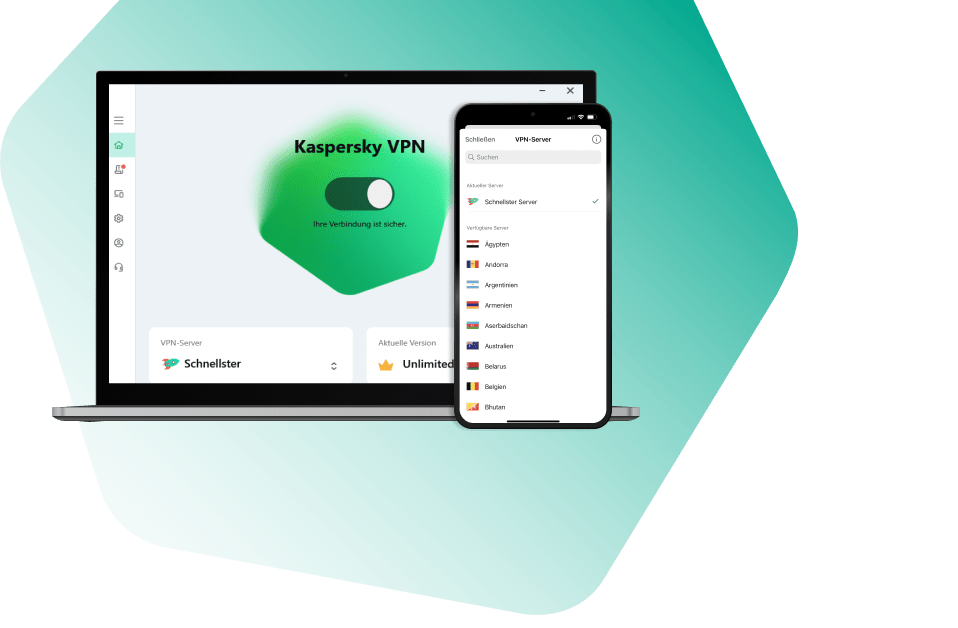
Kaspersky VPN Secure Connection
Sicher. Privat. Außergewöhnlich schnell. So sollte Internet sein.

Kaspersky Standard
Mejora la protección con el optimizador del rendimiento del dispositivo

Kaspersky Plus
Seguridad. Rendimiento. Privacidad. Todo en una única aplicación fácil de usar.

Kaspersky Small Office Security
Proteja fácilmente su pequeña empresa

Versión premium
Kaspersky Safe Kids
Supervisa a tus hijos, incluso cuando no estés con ellos

Kaspersky Small Office Security
Protégez votre PME sans effort

Kaspersky Plus
Combina recursos de segurança, desempenho e privacidade em um aplicativo

Kaspersky Small Office Security
Proteja a sua pequena empresa sem esforço

Kaspersky Premium
Proteção completa para seus dispositivos, privacidade online e identidade

Versão Premium
Kaspersky Safe Kids
Fique de olho nas crianças, mesmo quando não estiver por perto
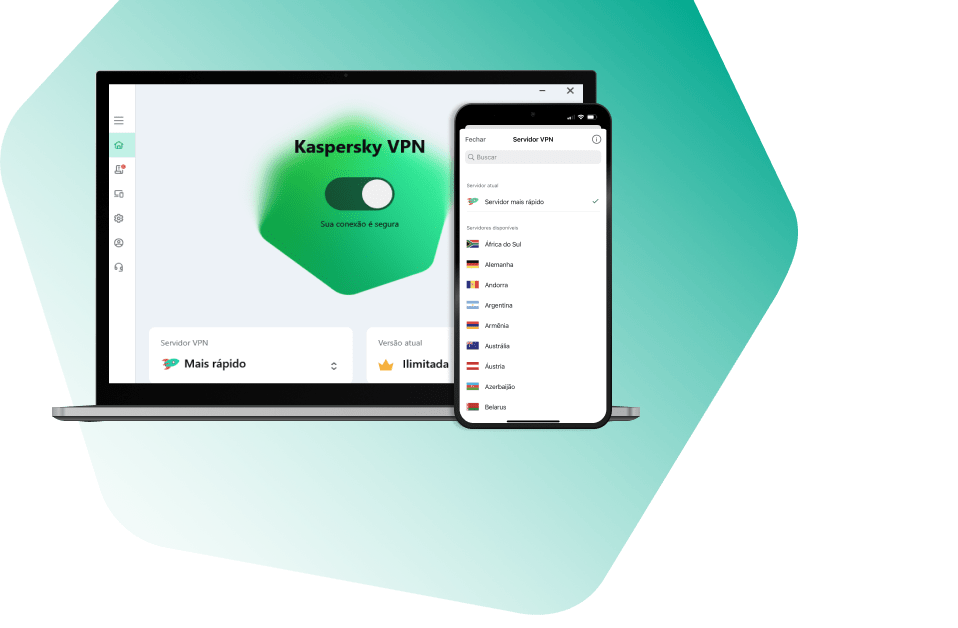
Kaspersky VPN Secure Connection
Segura. Privada. Excepcionalmente rápida. Como a internet deveria ser.

Kaspersky Standard
Protezione avanzata con ottimizzazione delle prestazioni dei dispositivi

Kaspersky Small Office Security
Protezione immediata delle piccole aziende

Versione premium
Kaspersky Safe Kids
Accertati che i tuoi figli siano al sicuro, anche quando non sei con loro

Kaspersky Secure Connection
Простое решение для защиты конфиденциальности и безопасности ценных данных
-
Forum
-
2
-
2
Получение serial number на rpi4 в KasperskyOS CE
Добрый день. Для текущего релиза 1.1.1.40 нельзя получить серийный номер. Мы можем рассмотреть добавление данной функциональности, но не могли бы вы, пожалуйста, предоставить краткое обоснование необходимости. -
1
Just found out from local "dealer" in my country, that there are no more licences for KAV and they are offering only for Kaspersky standard/plus/premium, among other Kaspersky products, which are not KAV and KIS.
Just found out from local "dealer" in my country, that there are no more licences for KAV and they are offering only for Kaspersky standard/plus/premium, among other Kaspersky products, which are not KAV and KIS. -
-
0
How to сheck KATA detects by different technologies(IOA, IDS, Sandbox) [KATA/KEDRE]
Advice and Solutions (Forum Knowledgebase) Disclaimer. Read before using materials. Problem Sometimes it's necessary to check KATA detects, for example IDS, IOA, Sandbox detects. Step-by-step guide IDS detects (SPAN) To check IDS detects (SPAN) you can use tcpreplay utility on server configured to receive SPAN traffic. KATA 4.0/4.1 tcpreplay package for such versions could be found here https://rhel.pkgs.org/7/epel-x86_64/tcpreplay-4.4.4-1.el7.x86_64.rpm.html KATA 5.+ and tcpreplay tcpreplay package is not installed by default, so you should install it manually, using step-by-step guide below: 1) Download this package from HERE 2) Place downloaded file tcpreplay_4.3.2-1build1_amd64.deb to your KATA node. For example, use scp: [user@host]$ scp <your-path>/tcpreplay_4.3.2-1build1_amd64.deb admin@<kata-ip>:/tmp 3) Run installation on your KATA node with the next command: [admin@katahost]$ sudo dpkg -i /tmp/tcpreplay_4.3.2-1build1_amd64.deb Success! Now you can use tcpreplay on your KATA 5.+ or any other UBUNTU system! Before using tcpreplay you should enable tx capture for span: KATA 3.7.* In technical support mode from user root run following commands : systemctl stop apt-preprocessor.service systemctl stop suricata.service rmmod pf_ring Edit file /etc/modprobe.d/pf_ring.conf: change line: options pf_ring enable_tx_capture=0 min_num_slots=16384 # tx capture is disabled to: options pf_ring enable_tx_capture=1 min_num_slots=16384 # tx capture is enabled save file. Start pfring and related services back: modprobe pf_ring systemctl start suricata.service systemctl start apt-preprocessor.service KATA 4.0/4.1 Edit file /etc/modprobe.d/pf_ring.conf: change line: options pf_ring enable_tx_capture=0 min_num_slots=16384 # tx capture is disabled to: options pf_ring enable_tx_capture=1 min_num_slots=16384 # tx capture is enabled save file. In technical support mode from user root run following commands: systemctl stop docker rmmod pf_ring modprobe pf_ring systemctl start docker tx capture for span is now enabled KATA 5.0/5.1/6.0 - see https://forum.kaspersky.com/topic/how-to-enable-tx-capturing-in-kata-katakedre-37514/ Eicar traffic detect: Upload EICAR-Test-File_TCP.pcap sample to server with SPAN interface, then execute command from root shell: tcpreplay -i ens34 EICAR-Test-File_TCP.pcap # ens34 in this example is SPAN interface Nmap traffic detect: Scenario is the same as for Eicar detect, only .pcap file differs (# tcpreplay HackTool.Nmap.HTTP.C&C.pcap). After testing detects from span we strongly recommend to disable tx capture back again by the same way as described above for enabling. AM Engine Use EICAR's - https://www.eicar.com/ Email - send the EICAR via SMTP to KATA 25 port. (SMTP processing needs to be Enabled of course). ProTip: you may use local swaks mail client on CN to skip elaborate mail setups. swaks examples swaks --server 127.0.0.1 --port 25 --from antony@test.org --to cleopatra@test.org --attach eicar.com swaks --server 127.0.0.1 --port 25 --from antony@test.org --to cleopatra@test.org --body "link_to_EICAR_here" Endpoint - put an EICAR file to the endpoint and fetch it using GetFile task, queue for scanning. YARA detects By default, no YARA rules are supplied with the product. For test purposes one can use a test rule from YARA docs https://yara.readthedocs.io/en/v4.1.0/writingrules.html rule ExampleRule { strings: $my_text_string = "text here" $my_hex_string = { E2 34 A1 C8 23 FB } condition: $my_text_string or $my_hex_string } The rule will mark any analyzed object containing $my_text_string or $my_hex_string. IoA detects To check IoA detect (IoA detects can be checked only if you have KEDR license): Copy .bat file from attached archive Test_IOA.rar(not_infected) to any folder on host with installed EDR and start it. After some time(KATA need several minutes to transmit and process telemetry from EDR) check alerts in KATA. Alert should have type ioa_test_detect. For testing IoA detects on host more than once, .bat file should be placed to different locations on this host. On the host with installed KEA run command below in the cmd.exe shell: wmic.exe sfdguninstallkasperskyblabla There can be something else instead of sdfg and blabla, important part of command is uninstallkaspersky Command execution will fail with error, but it's not important. After some time new IoA detect should appear in KATA web-interface. IoC detects One can use the custom rule for testing - Ioctest.zip (infected123) - it is triggered for "c:\windows\system32\calc.exe" Automatic sandboxing in EDR To check automatic sandboxing: Unpack the archive with sample, use default password for samples: autosbtest.zip NB! Do not change MD5 of the sample. Run the sample on EDR-protected host and wait for automatic SB detect: Sandbox detect To check sandbox detect we can use file SA_sleep.exe from archive no_am_detection sample.rar. Password is inside text document in archive. Go to KATA senior security officer web-interface. Choose Storage → Upload and upload SA_sleep.exe from attached archive for KATA checking. Kata should enqueue it to sandbox , then a bit later verdict from SB should be Suspicious Activity. If SA_sleep.exe produces Not detected verdict then please use test_sb.bat from the test_sb.rar URL reputation Firstly, confirm K(P)SN is configured and works properly. MD5 used in this example should return UnTrusted status: Check KSN on KATA command for KATA 4.+ and 5.0: docker exec -it `docker ps | grep ksn_proxy| awk '{print $1}'` /opt/kaspersky/apt-ksn_proxy/sbin/ksn_client --ip 127.0.0.1 --hash 9C642C5B111EE85A6BCCFFC7AF896A51 for KATA 5.1: docker exec -it $(docker ps | grep ksn_proxy| awk '{print $1}') /opt/kaspersky/apt-ksn-proxy/sbin/ksn_client --ip 127.0.0.1 --hash 9C642C5B111EE85A6BCCFFC7AF896A51 Secondly, For traffic: access http://bug.qainfo.ru/TesT/Aphish_w/index For email (SMTP processing needs to be Enabled), send the link above via e-mail. For quick and dirty test: swaks examples swaks --server 127.0.0.1 --port 25 --from fisherman@test.org --to cleopatra@test.org --body "http://bug.qainfo.ru/TesT/Aphish_w/index" -
2
-
64
-
1
what access do they have if my friends/family share device now
what access do they have if my friends/family share device now
-









